Each trend page maps macro region signals into industry-level execution intelligence.

Market / Trends
Trends
Navigation is fixed as Trends -> Region -> Industry. Each region carries an intelligence summary page and each industry has a dedicated route for structured trend analysis.
Global plus five geographic routes aligned to the market taxonomy.
Cloud Service, Regional ISP, National Telecom, Datacenter, and Institutional.
Pages are designed for stable trend navigation rather than single-run article chronology.
Taxonomy
Trend Regions
Region
Global
Cross-region intelligence baseline and macro structural signals.
Region
North America
Execution speed, policy enforcement, and platform operating leverage.
Region
Europe and Middle East
Compliance-driven market adjustment and governance coupling pressure.
Region
Asia-Pacific
IPv4 scarcity economics, scaling demand, and operational modernization.
Region
Latin America and Caribbean
Connectivity expansion, regulatory transition, and asset-efficiency pressure.
Region
Africa
Governance normalization, infrastructure financing, and growth asymmetry.
Latest Coverage
Trends Headlines
NATO’s $1.1B innovation fund invests in AI, robots and space tech
OUR TAKE The move further highlights the ability of NATO allies to cooperate and innovate in addressing modern security challenges, with the aim of ensuring that alliance members maintain strategic superiority and readiness in the face of increasingly sophisticated threats.–Revel Cheng, BTW reporter…
The historical evolution of the video game
One of the earliest examples of an electronic game is The Nim Number Game (Nim), a mathematical strategy game created in 1940.
Bayer looks to AI to combat herbicide resistance faster
OUR TAKE In addition to technological innovations, Bayer is also strengthening its cooperation with farmers and agricultural experts to develop more sustainable and environmentally friendly solutions. Their efforts are not only to introduce new products, but also to provide long-term ecological bala…
Archive
Trends Article Archive
9,023 articles

Trends
NATO’s $1.1B innovation fund invests in AI, robots and space tech
OUR TAKE The move further highlights the ability of NATO allies to cooperate and innovate in addressing modern security challenges, with the aim of ensuring …

Trends
The historical evolution of the video game
One of the earliest examples of an electronic game is The Nim Number Game (Nim), a mathematical strategy game created in 1940.

Trends
Bayer looks to AI to combat herbicide resistance faster
OUR TAKE In addition to technological innovations, Bayer is also strengthening its cooperation with farmers and agricultural experts to develop more sustaina…

Trends
Understanding 3 threats to computer security
Cybersecurity is an ever-evolving field, and understanding the various types of threats is crucial for both individuals and businesses. As we become more rel…

Trends
Computer security vs. information security: What’s the difference?
With the increasing reliance on technology, the terms “computer security” and “information security” are often used interchangeably. However, these concepts,…

Trends
5 must-know elements of computer security
Your quick guide to staying safe online In a world where digital threats are ever-present, mastering computer security is a must. Let’s dive into the five es…
Trends
Spotting the hooks: 5 common indicators of a phishing attempt
phishing attempts often contain multiple spelling and grammatical errors, which can indicate a fraudulent email.
Trends
U.S. urges allies to tighten control over Chinese semiconductors
U.S. officials are urging Dutch and Japanese counterparts to controls on China’s semiconductor, aiming to restrict Chinese advancements.

Trends
The 4 types of phishing
Phishing targeted at specific individuals to deceive recipients into disclosing sensitive data like passwords or financial information.

Trends
Whale phishing: How cybercriminals target high-flyers
Whale phishing is a sophisticated cyber threat specifically aimed at high-profile individuals such as executives, CEOs within organisations.
Trends
What screams ‘phishing scam’? Recognising unmistakable signs
One of the most recognisable signs of a phishing attempt is an email sender address that doesn’t match the identity.

Trends
Clone phishing: The sneaky scam targeting your inbox
Clone phishing poses significant risks to both individuals and organisations, manifesting in various severe consequences.
Trends
Unmasking online threats: The power of anti-phishing technology
Email filtering and security gateways play a crucial role in preventing phishing attacks by identifying and mitigating threats.

Trends
Arm yourself against phishing: Proven prevention techniques
Phishing attacks are a type of cyberattack where malicious actors impersonate legitimate entities to deceive individuals.
Trends
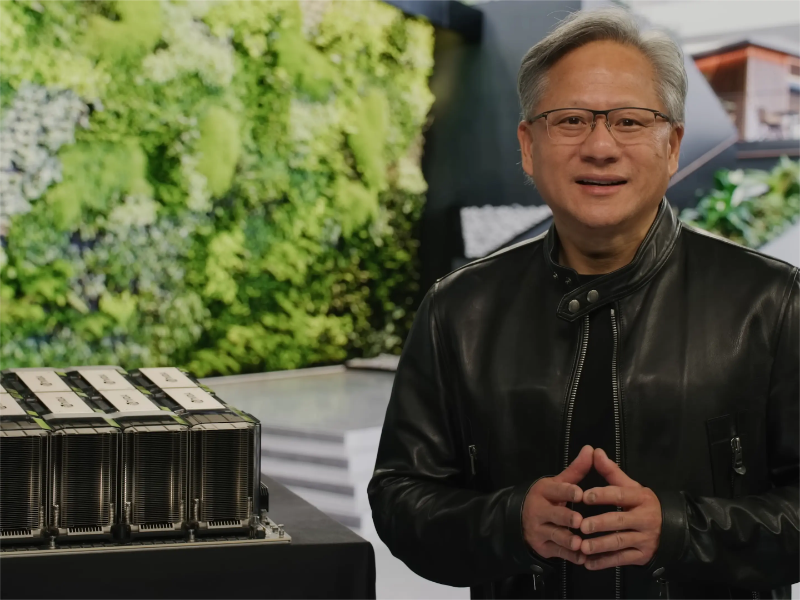
Nvidia surges to become world’s most valuable company
OUR TAKENvidia’s astonishing ascent is more than a financial milestone—it’s a testament to human ingenuity and the transformative power of AI. Their journey …

Trends
AMD is investigating a suspected data breach crisis
Advanced Micro Devices Inc is investigating allegations that its company information was stolen in a cyberattack.

Trends
Cracking the code: Spam vs. phishing
The key differences between spam and phishing include their objective, content, targeting, detection and prevention and consequences.

Trends
Don’t take the bait: How to identify phishing emails?
We can detect it by being careful while answering public domain emails, avoiding misspelled domain names and spotting poorly written emails.
Trends
DMZ Network: Definition, working principles and benefits
Public websites need accessible web servers, separated from internal networks in a DMZ with strong security measures.

Trends
How to invest in Databricks?
Investors, even if Databricks isn’t publicly traded, can engage in its growth through platforms like EquityBee or Forge Global.
