DMZ Network: Definition, working principles and benefits is profiled by BTW Media because published evidence links it to internet infrastructure, governance, operational dependencies, or market visibility.
DMZ Network: Definition, working principles and benefits is tracked as a internet infrastructure institution within the internet infrastructure ecosystem.
DMZ Network: Definition, working principles and benefits has public-source relevance to network operations, governance, dependency mapping, or market structure.
DMZ Network: Definition, working principles and benefits has public-source relevance to network operations, governance, dependency mapping, or market structure.
DMZ Network: Definition, working principles and benefits is tracked as a internet infrastructure institution within the internet infrastructure ecosystem.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
DMZ Network: Definition, working principles and benefits is profiled by BTW Media because published evidence links it to internet infrastructure, governance, operational dependencies, or market visibility.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
| 0.90–1.00 | A | High — direct sources |
| 0.75–0.89 | A/B | Strong |
| 0.55–0.74 | B/C | Medium |
| 0.35–0.54 | C/D | Weak–medium |
| 0.10–0.34 | D | Weak signal |
| 0.00–0.09 | D | Internal monitoring |
Several public sources
- A demilitarised zone is a perimeter network that shields an organisation’s internal LAN from untrusted traffic
- Public websites need accessible web servers, separated from internal networks in a DMZ with strong security measures.
This article will introduce the definition, working principles and benefits of DMZ network.
What is a DMZ Network?
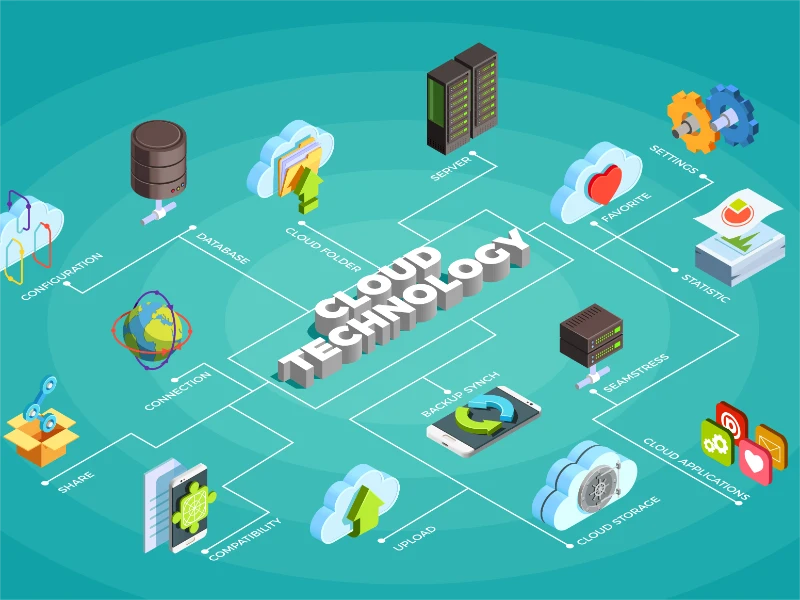
A DMZ, also known as a demilitarised zone, serves as an intermediary network that shields an organisation’s internal LAN from untrusted traffic, bolstering security. The primary objective of a DMZ network is to enable access to untrusted networks like the internet while safeguarding the security of the organisation’s private LAN. Typically, external-facing services and essential servers such as DNS, FTP, mail, proxy, VoIP, and web servers are housed within the DMZ for enhanced security measures.
Also read: 3 key security risks of cloud computing
Also read: The most pressing cybersecurity threats
How does it work?
Businesses operating public websites for customer use need their web servers accessible on the internet. To safeguard their internal corporate networks, these web servers are deployed on separate computers isolated from internal resources. The DMZ facilitates secure communication between protected business assets, like internal databases, and authorised traffic from the internet. A DMZ network acts as a buffer between the internet and the organisation’s private network, secured by a firewall or similar security gateway that filters traffic between the DMZ and the LAN.
The DMZ typically includes servers protected by another firewall that filters incoming traffic from external networks.
Ideally positioned between two firewalls, the DMZ setup ensures that incoming network packets are scrutinised by security measures before reaching servers hosted within the DMZ. This setup imposes an additional layer of defence: even if an attacker breaches the external firewall, they must then compromise the hardened services within the DMZ before gaining access to critical business systems. In the event of a breach where an attacker penetrates the external firewall and compromises a DMZ system, they must still navigate through an internal firewall to reach sensitive corporate data.
Although skilled attackers might breach a secure DMZ, internal resources within it should trigger alerts, providing early warning of any ongoing breach. Organisations adhering to regulatory requirements, such as HIPAA, may deploy a proxy server in the DMZ. This simplifies monitoring and recording of user activity, centralises web content filtering, and ensures employees access the internet securely through controlled systems.
Benefits of using it
The main benefit of a DMZ is to offer an internal network with an advanced security layer by restricting access to sensitive data and servers.
- Facilitating access control: Businesses enable user access to external services via the public internet while employing network segmentation through the DMZ to hinder unauthorised access to the private network. A DMZ may incorporate a proxy server to centralise internal traffic flow and streamline monitoring and logging of such activities.
- Thwarting network reconnaissance: Positioned as a buffer between the internet and a private network, a DMZ prevents attackers from conducting reconnaissance to identify potential targets. Servers in the DMZ are exposed publicly but protected by a firewall that obstructs visibility into the internal network. Even if a DMZ server is compromised, an internal firewall isolates the private network from the DMZ, enhancing security and complicating external reconnaissance efforts.
At A Glance
- Name: DMZ Network: Definition, working principles and benefits
- Type: Internet infrastructure institution
- Base: Global
- Profile focus: Institution
What It Does
- Public records support monitoring of its role, services, and key relationships.
Why It Matters
- Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
- Operational criticality: Medium
- Time horizon: Next quarter
What To Watch
- Monitoring focuses on verified service continuity, governance changes, and relationship signals.
Track verified source updates, role changes, and current public evidence.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
Longer-term relevance depends on verified operating, policy, and relationship changes.
Member Briefing
Deeper Profile Context
Login is required to unlock the full profile briefing and source notes.
Only for Strategy Circle
Strategic Circle Access
Open to all readers. Unlock profile briefings after joining and logging in.
Join Strategic CircleOnly for Leadership Alliance
Leadership Alliance Access
For owners and management of IP-holding companies. Login required to unlock.
Join Leadership Alliance