The difference between a vulnerability and an exploit is profiled by BTW Media because published evidence links it to internet infrastructure, governance, operational dependencies, or market visibility.
The difference between a vulnerability and an exploit is tracked as a internet infrastructure institution within the internet infrastructure ecosystem.
The difference between a vulnerability and an exploit has public-source relevance to network operations, governance, dependency mapping, or market structure.
The difference between a vulnerability and an exploit has public-source relevance to network operations, governance, dependency mapping, or market structure.
The difference between a vulnerability and an exploit is tracked as a internet infrastructure institution within the internet infrastructure ecosystem.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
The difference between a vulnerability and an exploit is profiled by BTW Media because published evidence links it to internet infrastructure, governance, operational dependencies, or market visibility.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
| 0.90–1.00 | A | High — direct sources |
| 0.75–0.89 | A/B | Strong |
| 0.55–0.74 | B/C | Medium |
| 0.35–0.54 | C/D | Weak–medium |
| 0.10–0.34 | D | Weak signal |
| 0.00–0.09 | D | Internal monitoring |
Several public sources
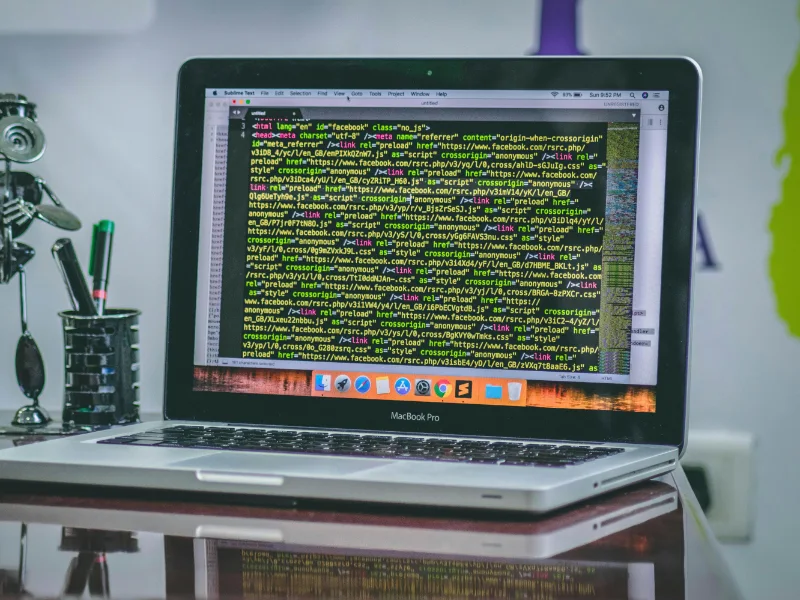
Vulnerability can occur during the construction and coding of technology. These mistakes often result in what is commonly known as a bug. Some bugs can be exploited by malicious actors, and these are referred to as vulnerabilities. Exploits are the methods by which a vulnerability can be utilised for malicious activities by hackers; these can include software components, sequences of commands, or even open-source exploit kits. In the realm of cybersecurity, vulnerabilities represent weaknesses in software, systems, or networks that can potentially be exploited by malicious actors. When these vulnerabilities are leveraged to compromise security, they become exploits. This distinction between vulnerability and exploit is crucial: vulnerabilities are the flaws, while exploits are the actions that take advantage of them. Understanding and mitigating vulnerabilities is essential in safeguarding against cyber threats and ensuring robust security measures. Also read: Security vulnerability uncovered in Apple Silicon chips Also read: GitHub Vulnerability Exposes 4,000+ to RepoJacking Attack What are vulnerabilities? Errors can occur during the construction and coding of technology. These mistakes often result in what is commonly known as a bug. Bugs are generally not harmful in themselves, although they can affect the performance of the technology. However, some bugs can be exploited by malicious actors, and these are referred to as vulnerabilities. Vulnerabilities can be manipulated to make software behave in unintended ways, such as extracting information about the current security defenses in place. What is an exploit? Exploitation is the subsequent stage in an attacker’s playbook following the discovery of a vulnerability. Exploits are the methods by which a vulnerability can be utilised for malicious activities by hackers; these can include software components, sequences of commands, or even open-source exploit kits. Differences between a vulnerability and an exploit There’s a straightforward way to distinguish between a vulnerability and an exploit. A vulnerability is a weak point in an IT system or programme. An exploit is the action of using that vulnerability to gain access to or compromise software or IT networks. An exploit cannot exist without a vulnerability, but vulnerabilities can exist that have never been exploited. These are known as zero-day vulnerabilities if and when they are exploited for the first time. The weakness is the vulnerability, whereas an exploit is the action of exploiting that weakness. Here are a few examples of vulnerabilities: 1.Weak passwords 2.Software that hasn’t been patched or updated 3.Weaknesses in programme or software code 4.Human responses to phishing attacks Some vulnerabilities are widely known, while others are only identified after being exploited. At Intrust, we aim to assist companies in reducing their vulnerabilities through a mix of endpoint protection, system monitoring, incident response, and cybersecurity training for your entire team. Zero-day vulnerabilities and exploits This term refers to a security flaw or weakness in software, hardware, or firmware that is publicly documented context to the vendor or developer. It is called “zero-day” because the developers have had zero days to fix or patch the issue since it became known to attackers. Essentially, it means the vulnerability is new and has not yet been discovered or publicly disclosed by the vendor.
At A Glance
- Name: The difference between a vulnerability and an exploit
- Type: Internet infrastructure institution
- Base: Global
- Profile focus: Institution
What It Does
- Public records support monitoring of its role, services, and key relationships.
Why It Matters
- Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
- Operational criticality: Medium
- Time horizon: Next quarter
What To Watch
- Monitoring focuses on verified service continuity, governance changes, and relationship signals.
Track verified source updates, role changes, and current public evidence.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
Longer-term relevance depends on verified operating, policy, and relationship changes.
Member Briefing
Deeper Profile Context
Login is required to unlock the full profile briefing and source notes.
Only for Strategy Circle
Strategic Circle Access
Open to all readers. Unlock profile briefings after joining and logging in.
Join Strategic CircleOnly for Leadership Alliance
Leadership Alliance Access
For owners and management of IP-holding companies. Login required to unlock.
Join Leadership Alliance