Preventing route leaks made simple: BGP roleplay with Junos is profiled by BTW Media because published evidence links it to internet infrastructure, governance, operational dependencies, or market visibility.
Preventing route leaks made simple: BGP roleplay with Junos is tracked as a internet infrastructure institution within the internet infrastructure ecosystem.
Preventing route leaks made simple: BGP roleplay with Junos has public-source relevance to network operations, governance, dependency mapping, or market structure.
Preventing route leaks made simple: BGP roleplay with Junos has public-source relevance to network operations, governance, dependency mapping, or market structure.
Preventing route leaks made simple: BGP roleplay with Junos is tracked as a internet infrastructure institution within the internet infrastructure ecosystem.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
Preventing route leaks made simple: BGP roleplay with Junos is profiled by BTW Media because published evidence links it to internet infrastructure, governance, operational dependencies, or market visibility.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
| 0.90–1.00 | A | High — direct sources |
| 0.75–0.89 | A/B | Strong |
| 0.55–0.74 | B/C | Medium |
| 0.35–0.54 | C/D | Weak–medium |
| 0.10–0.34 | D | Weak signal |
| 0.00–0.09 | D | Internal monitoring |
Several public sources
- BGP roleplay in Junos now supports RFC 9234, offering simplified route management.
- The new feature addresses long-standing issues of accidental route leaks in large networks.
What happened: New BGP tweak promises to prevent route leaks with RFC 9234
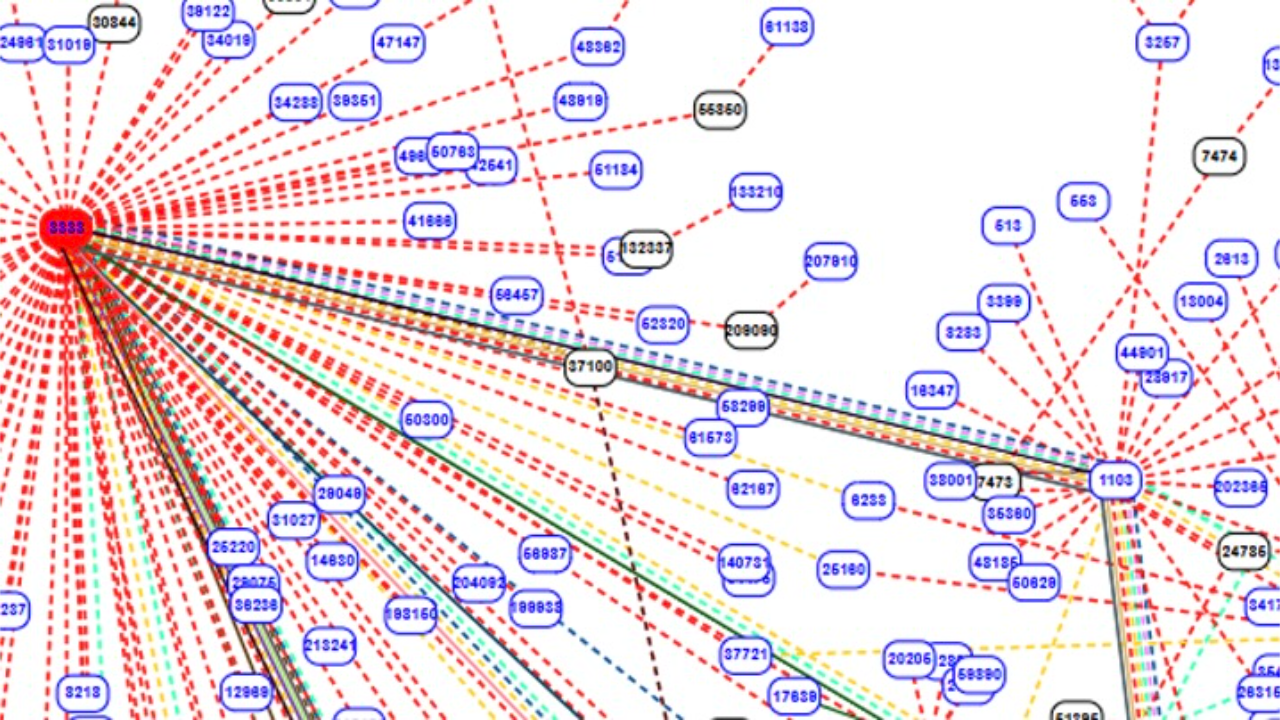
Border Gateway Protocol (BGP) has long been a source of network instability, with accidental route leaks and hijacks being common occurrences. This problem has persisted since BGP’s inception over three decades ago. However, a simple yet crucial tweak, defined in RFC 9234, aims to address this issue effectively. The RFC introduces the “Only-To-Customer” (OTC) BGP Capability, which significantly reduces the risk of these leaks by assigning roles to Autonomous Systems (ASes) in a network, ensuring that routes are only advertised to the intended recipients.
The feature has already been implemented by Quagga/FRR, with a patch available for BIRD. Notably, Juniper’s Junos OS now supports this capability, marking a major milestone in the adoption of RFC 9234. This innovation allows for more precise control over route advertisement, preventing accidental leaks by enforcing strict role-based policies on how networks interact.
Also Read: How AFRINIC’s board elections became a political battlefield
Also Read: Why AFRINIC’s fallout has global implications for internet governance
Why it’s important
The importance of RFC 9234 cannot be overstated in the context of BGP route management. Traditionally, operators used complex routing policies to define how routes should be shared between providers, peers, and customers. However, these manual configurations were prone to errors, especially in large-scale networks with hundreds or thousands of BGP neighbours.
RFC 9234 simplifies the process by automating role assignment, helping prevent errors that lead to route leaks. For example, when an AS mistakenly advertises routes to a peer that should only be available to a customer, it can lead to severe network disruptions, including BGP hijacking. With the new OTC role, these routes can be automatically blocked from being advertised outside their intended scope.
This development is particularly crucial for Tier 1 and Tier 2 network operators, who manage vast and complex networks. It promises a more streamlined and error-resistant BGP management system, improving the reliability of the internet backbone.
However, while the solution is a step forward, it may not be a complete fix for all BGP-related issues. Network operators still need to ensure they implement other safeguards, such as the principles outlined in RFC 8212 and the MANRS initiative, for comprehensive routing security.
At A Glance
- Name: Preventing route leaks made simple: BGP roleplay with Junos
- Type: Internet infrastructure institution
- Base: Africa
- Profile focus: Institution
What It Does
- Public records support monitoring of its role, services, and key relationships.
Why It Matters
- Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
- Operational criticality: Medium
- Time horizon: Next quarter
What To Watch
- Monitoring focuses on verified service continuity, governance changes, and relationship signals.
Track verified source updates, role changes, and current public evidence.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
Longer-term relevance depends on verified operating, policy, and relationship changes.
Member Briefing
Deeper Profile Context
Login is required to unlock the full profile briefing and source notes.
Only for Strategy Circle
Strategic Circle Access
Open to all readers. Unlock profile briefings after joining and logging in.
Join Strategic CircleOnly for Leadership Alliance
Leadership Alliance Access
For owners and management of IP-holding companies. Login required to unlock.
Join Leadership Alliance