Each trend page maps macro region signals into industry-level execution intelligence.

Market / Trends
Trends
Navigation is fixed as Trends -> Region -> Industry. Each region carries an intelligence summary page and each industry has a dedicated route for structured trend analysis.
Global plus five geographic routes aligned to the market taxonomy.
Cloud Service, Regional ISP, National Telecom, Datacenter, and Institutional.
Pages are designed for stable trend navigation rather than single-run article chronology.
Taxonomy
Trend Regions
Region
Global
Cross-region intelligence baseline and macro structural signals.
Region
North America
Execution speed, policy enforcement, and platform operating leverage.
Region
Europe and Middle East
Compliance-driven market adjustment and governance coupling pressure.
Region
Asia-Pacific
IPv4 scarcity economics, scaling demand, and operational modernization.
Region
Latin America and Caribbean
Connectivity expansion, regulatory transition, and asset-efficiency pressure.
Region
Africa
Governance normalization, infrastructure financing, and growth asymmetry.
Latest Coverage
Trends Headlines
Why is fintech disrupting traditional banking?
Fintech has changed consumer expectations and improved service quality through innovative technology applications and service models.
Is deepfake AI illegal?
Deepfake uses deep learning for image synthesis to create falsified videos, and when used maliciously without consent may cause legal risks.
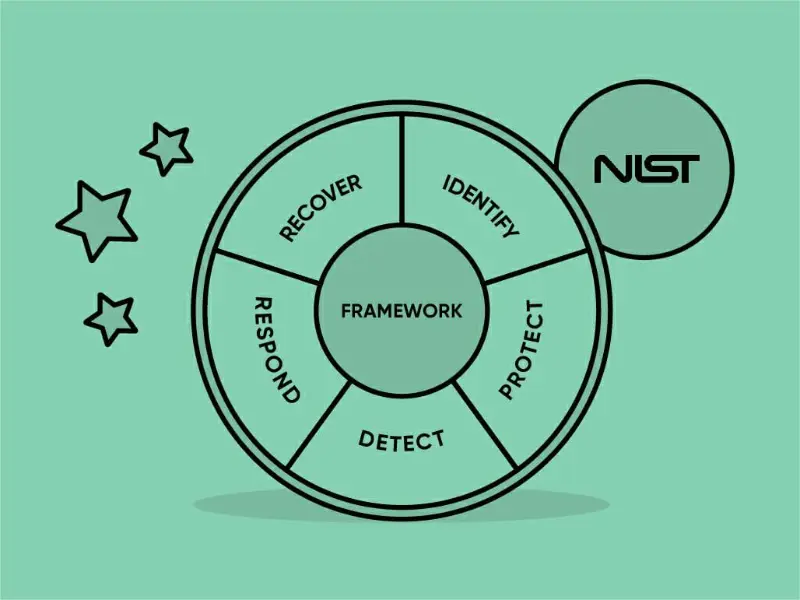
What are the main components of the NIST cybersecurity framework?
The NIST CSF is a set of guidelines for mitigating organisations’ cybersecurity risks. The main components are “Core”, “Profile” and “Tiers”.
Archive
Trends Article Archive
9,189 articles

Trends
Why is fintech disrupting traditional banking?
Fintech has changed consumer expectations and improved service quality through innovative technology applications and service models.

Trends
Is deepfake AI illegal?
Deepfake uses deep learning for image synthesis to create falsified videos, and when used maliciously without consent may cause legal risks.
Trends
What are the main components of the NIST cybersecurity framework?
The NIST CSF is a set of guidelines for mitigating organisations’ cybersecurity risks. The main components are “Core”, “Profile” and “Tiers”.

Trends
Why is cybersecurity important in healthcare?
Cybersecurity in healthcare is critical for patient data privacy and regulatory compliance. The HIPAA provides a structured approach.

Trends
What is cybersecurity compliance?
Cybersecurity compliance ensures organisation adheres to related industry standards and global regulations on data privacy.

Trends
How to create a large language model (LLM)?
LLMs are AI models that generate textual content. Creating LLMs requires computer science expertise and adherence to ethics.

Trends
How does a client server infrastructure work?
Client devices interact with centralised servers to access services and data in a client-server infrastructure.

Trends
Why is it so challenging to secure digital information?
Human error and social engineering tactics contribute to security risks and vulnerabilities in cybersecurity.
Trends
How is information transmitted and exchanged using the internet?
Data packets traverse various networks, such as LANs, WANs, and the Internet backbone, interconnected through ISPs and peering agreements.

Trends
What is an example of a supercomputer?
The supercomputer helps researchers analyse large datasets and visualize complex information for better understanding.
Trends
How does satellite technology work?
Scientific research satellites enable studies in astronomy, Earth sciences, climate, and space exploration.

Trends
True IDC shines at Veeam Partner Appreciation Day 2024
True IDC, a prominent provider of data center and cloud services in Thailand, recently secured significant recognition at the Veeam Partner Appreciation Day …

Trends
Meta releases early versions of Llama 3 multimodal AI model
Meta Platforms released early versions of its latest large language model, Llama 3, with new computer coding capabilities and the ability to process image co…

Trends
China acquired banned Nvidia chips in Super Micro, Dell servers
Chinese universities and research institutions have recently obtained high-end Nvidia chips that were banned from being sold to China by US.

Trends
Why is cybersecurity important?
Cybersecurity includes all technologies and practices that ensure the security of computer systems and electronic data.

Trends
Is cybersecurity becoming too saturated?
In recent years, the question “Is cybersecurity oversaturated?” The issue has sparked considerable debate.

Trends
5 best AI video generators
Artificial intelligence can generate voice-overs based on your own scripts by finding and combining videos, images, and music.
Trends
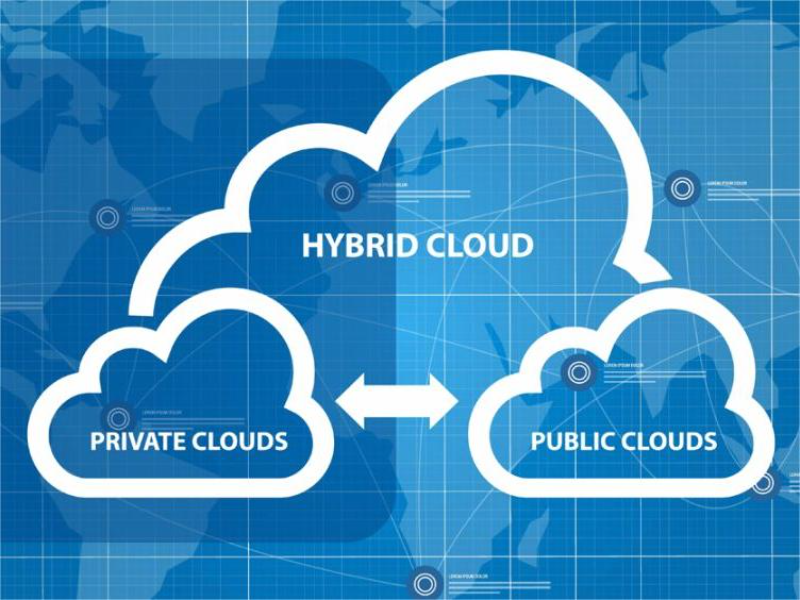
What is hybrid cloud architecture?
Hybrid cloud architecture refers to an environment that combines on-premises, private cloud, public cloud, and edge Settings
Trends
Microsoft launches lightweight AI model Phi-3-mini
Microsoft launched the next version of its lightweight AI model, Phi-3 Mini, the first of three smaller models the company plans to release. The move marks t…

Trends
What is cybersecurity risk management?
According to Dave Hatter, a cybersecurity consultant at Intrust IT, “As more of our physical world is connected to and controlled by the virtual world, and m…
