Can multi-factor authentication be hacked? is profiled by BTW Media because published evidence links it to internet infrastructure, governance, operational dependencies, or market visibility.
Can multi-factor authentication be hacked? is tracked as a internet infrastructure institution within the internet infrastructure ecosystem.
Can multi-factor authentication be hacked? has public-source relevance to network operations, governance, dependency mapping, or market structure.
Can multi-factor authentication be hacked? has public-source relevance to network operations, governance, dependency mapping, or market structure.
Can multi-factor authentication be hacked? is tracked as a internet infrastructure institution within the internet infrastructure ecosystem.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
Can multi-factor authentication be hacked? is profiled by BTW Media because published evidence links it to internet infrastructure, governance, operational dependencies, or market visibility.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
| 0.90–1.00 | A | High — direct sources |
| 0.75–0.89 | A/B | Strong |
| 0.55–0.74 | B/C | Medium |
| 0.35–0.54 | C/D | Weak–medium |
| 0.10–0.34 | D | Weak signal |
| 0.00–0.09 | D | Internal monitoring |
Several public sources
- Like bitcoin ETFs, Ethereum ETFs offer investors a convenient means of gaining access to a cryptocurrency without having to hold the digital asset directly.
- Multi-factor authentication can be hacked through four ways: social engineering, spoofed landing page, session hijacking, and SIM swap.
- You could protect your business from MFA by setting up your MFA with robust policies and using hardware keys.
Multi-factor authentication (MFA) is the process of a user or device providing two or more different types of proofs of control associated with a specific digital identity, to gain access to the associated permissions, rights, privileges, and memberships. Two-factor authentication (2FA) implies that exactly two proofs are required for a successful authentication, and is a subset of MFA.
Understanding how MFA works requires a broader understanding of the concept of authentication. In an identity access management (IAM) framework, authentication factors are security mechanisms used to prove a user is who they claim to be before they’re allowed access to privileged information.
There are three types of authentication factors: knowledge factors, possession factors, and inherence factors.
MFA requires users to prove at least two of these factors to verify their identity.
How hackers can bypass multi-factor authentication?
Social engineering
Social engineering involves tricking a victim into revealing privileged information that can be leveraged in a cyber attack. This attack method is most commonly used when the attacker has already compromised a victim’s username and password and needs to bypass additional authentication factors.
In this instance, an attacker will pose as “someone from IT” or another trusted user. They will then use this position of trust to manipulate users into sharing important account details. Once the user has given over their details, the attacker can access their account and your corporate network. They might even change that user’s password, meaning that they lose access to the account.
These attackers might warn a user that their account has already been hacked, or is at risk of being hacked if they don’t share their details with the “trusted user” who can act to prevent this. Ironically, this leads users to give the hacker everything they need to bypass their MFA and infiltrate their corporate network.
Spoofed landing page
A spoofed landing page is a fraudulent site that is designed to look like a reputable, trusted site that you already know and use. It could be LinkedIn, Facebook, Gmail, or another popular site. When you attempt to log in on this site, your access will be denied, and your account details will be stored by the malicious actors. The malicious actor can then use the details that you have provided to bypass the MFA security on the genuine website or account.
Also read: AI: The opportunities and the threats
Session hijacking
Session hijacking (or cookie stealing) occurs when a cybercriminal compromises a user’s login session through a man-in-the-middle attack. Session cookies play an important role in UX on web services.
When a user logs into an online account, the session cookie contains the user’s authentication credentials and tracks their session activity. The cookie remains active until the user ends the session by logging out.
Session hijacking is possible when a web server doesn’t flag session cookies as secure. If users don’t send cookies back to the server over HTTPS, attackers can steal the cookie and hijack the session, bypassing MFA.
SIM swap
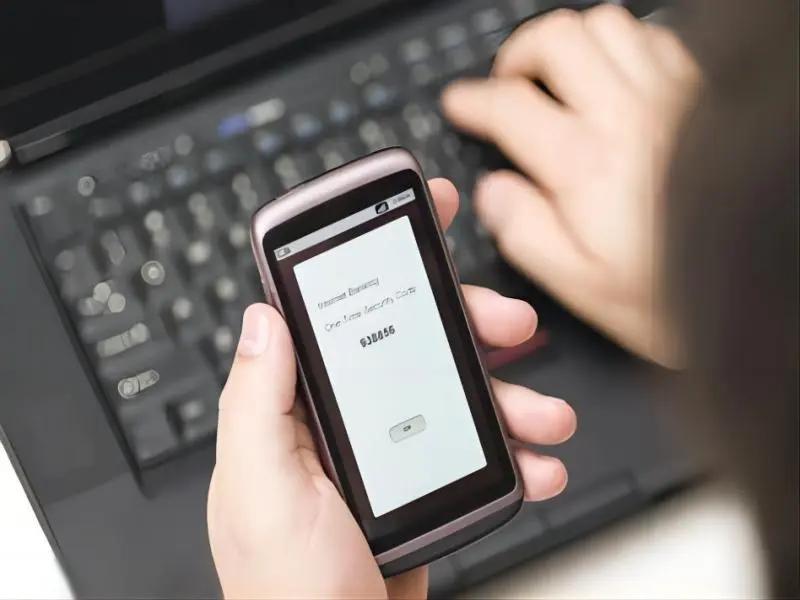
One-time passcodes (OTPs) are a common way of verifying identity by MFA solutions. This is usually a six- or eight-digit code sent to you via SMS. By entering the code, you verify that you have the cell phone that is linked to the named user, which suggests that your identity is authentic.
Hackers can, however, contact your mobile provider and convince them to perform a SIM swap. This will result in the messages intended for the user, being redirected to the hacker. They can then access your account using the verification code that was intended for you. It takes a degree of social engineering to persuade the mobile carrier to change the SIM; the hackers will also have to know the rest of your account details before attempting this method. They could obtain these details on the dark web, using a database of credentials harvested during a previous data breach, or by using a spoofed landing page.
Also read: What is Perplexity AI?
How can you protect your business from MFA hacking?
MFA set up
By setting up your MFA with robust policies, you can increase the strength of protection guarding your users’ accounts. Biometric factors – like fingerprint sensors, faceID, and typing analysis – are the hardest factors to impersonate and will therefore make it much harder for hackers to infiltrate your accounts. Incorporating contextual and behavioural analysis can also help to prevent unwanted intrusion. This logs factors such as a user’s usual location and login times. Any logins that do not fit with the pattern of expected behaviour will be flagged as suspicious and stopped.
Hardware authentication keys
Hardware keys, particularly ones that utilise FIDO 2 principles, are some of the most secure identification methods. It is very difficult for a hacker to gain access to the information, and the physical hardware that is required for this type of attack. Hardware keys are often designed to be tamper-proof to ensure your account is kept safe. FIDO 2 is a passwordless standard that is easy to use, and very secure. It uses public-key cryptography, which makes it virtually impossible for a hacker to find a way to access your account.
You may be wondering why MFA is even necessary after reading this article considering how easily it can be compromised. It is accurate to say that no cybersecurity solution can ensure complete impenetrability. Hackers are always looking for openings in systems and methods to gain access to private information. On the other hand, an account with MFA will be far more difficult to hack than one without.
At A Glance
- Name: Can multi-factor authentication be hacked?
- Type: Internet infrastructure institution
- Base: Global
- Profile focus: Institution
What It Does
- Public records support monitoring of its role, services, and key relationships.
Why It Matters
- Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
- Operational criticality: Medium
- Time horizon: Next quarter
What To Watch
- Monitoring focuses on verified service continuity, governance changes, and relationship signals.
Track verified source updates, role changes, and current public evidence.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
Longer-term relevance depends on verified operating, policy, and relationship changes.
Member Briefing
Deeper Profile Context
Login is required to unlock the full profile briefing and source notes.
Only for Strategy Circle
Strategic Circle Access
Open to all readers. Unlock profile briefings after joining and logging in.
Join Strategic CircleOnly for Leadership Alliance
Leadership Alliance Access
For owners and management of IP-holding companies. Login required to unlock.
Join Leadership Alliance