4 network devices that secure API connections is profiled by BTW Media because published evidence links it to internet infrastructure, governance, operational dependencies, or market visibility.
4 network devices that secure API connections is tracked as a internet infrastructure institution within the internet infrastructure ecosystem.
4 network devices that secure API connections has public-source relevance to network operations, governance, dependency mapping, or market structure.
4 network devices that secure API connections has public-source relevance to network operations, governance, dependency mapping, or market structure.
4 network devices that secure API connections is tracked as a internet infrastructure institution within the internet infrastructure ecosystem.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
4 network devices that secure API connections is profiled by BTW Media because published evidence links it to internet infrastructure, governance, operational dependencies, or market visibility.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
| 0.90–1.00 | A | High — direct sources |
| 0.75–0.89 | A/B | Strong |
| 0.55–0.74 | B/C | Medium |
| 0.35–0.54 | C/D | Weak–medium |
| 0.10–0.34 | D | Weak signal |
| 0.00–0.09 | D | Internal monitoring |
Several public sources
- APIs (Application Programming Interfaces) are integral to modern software development and are commonly used to enable communication between different systems and applications.
- Firewalls are essential network security devices that monitor and control incoming and outgoing traffic based on predefined security rules.
- IDPS systems are designed to detect and prevent unauthorised access or malicious activities within a network.
OUR TAKE
While devices play a crucial role in securing APIs, they present various challenges related to integration, scalability, accuracy, compliance, interoperability, and keeping up with evolving threats. Addressing these challenges requires a comprehensive and well-coordinated approach to API security. Designing a device that completely blocks all threats is difficult, expensive, and still takes a long time.
–Miurio, BTW reporter
APIs (Application Programming Interfaces) are integral to modern software development and are commonly used to enable communication between different systems and applications. That is the reason why we should improve our awareness of securing API.
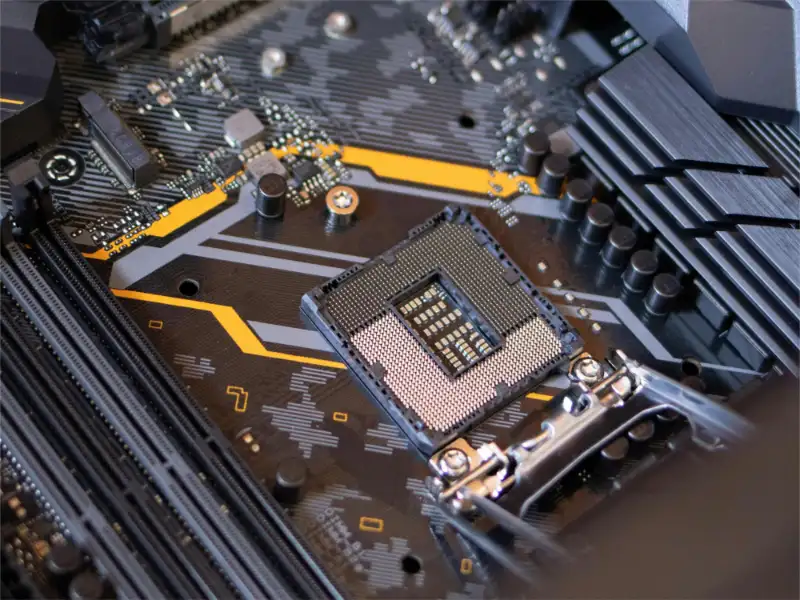
1. Firewalls
Firewalls are essential network security devices that monitor and control incoming and outgoing traffic based on predefined security rules. They can be configured to allow or block specific API requests, ensuring only authorised traffic reaches the API platform.
Some applications have their own firewalls. Web Application Firewalls (WAF) are specifically designed to protect web applications, from common web-based attacks such as SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF). They inspect and filter API requests, mitigating potential vulnerabilities.
Also read: 8 steps to do API integration
Also read: What is API integration?
2. Intrusion detection and prevention systems (IDPS)
IDPS systems are designed to detect and prevent unauthorised access or malicious activities within a network.
IDPS provide comprehensive real-time monitoring of API traffic, detecting unusual patterns or anomalies by examining request rates, payload sizes, and call frequencies. They use signature-based detection to identify known threats by comparing requests against a database of attack patterns, helping to spot common vulnerabilities like SQL injection and XSS. Anomaly-based detection establishes a baseline of normal usage to identify deviations, enabling the detection of zero-day or novel attacks. By analysing user and application behavior, IDPS can flag unusual activities, such as unexpected spikes in requests or access from unfamiliar locations. To prevent abuse and denial-of-service attacks, IDPS implements rate limiting and throttling, ensuring no single entity overwhelms the API. When threats are detected, IDPS generates alerts and detailed reports for security teams to investigate, providing information on the nature of threats, source IPs, and affected endpoints. Automated responses can further mitigate threats by blocking malicious IP addresses and terminating suspicious sessions. IDPS also logs all incidents for forensic analysis, helping understand attack nature and impacts, and supports regulatory compliance by providing detailed monitoring and reporting. Integration with other security tools, such as Web Application Firewalls, SIEM systems, and endpoint security solutions, enhances the overall security ecosystem.
3. Virtual private networks (VPNs)
VPNs establish secure connections over public networks, encrypting data traffic between the client and the API platform. By using VPNs, the API platform can ensure that data transmitted between the client and server remains confidential and protected from eavesdropping.
VPNs use robust encryption protocols like IPsec or SSL or TLS to secure data transmitted between clients and servers, protecting API communications from unauthorised interception. They implement strict authentication measures, including usernames, passwords, digital certificates, and multi-factor authentication, to ensure only authorised users and devices can access the network and associated APIs. VPNs create secure communication channels that encrypt and encapsulate data packets to prevent eavesdropping and manipulation, thwarting man-in-the-middle attacks. Additionally, they enable IP whitelisting within the VPN network to restrict API access, reducing exposure and unauthorised access risks. By facilitating network segmentation and granular access control, VPNs isolate critical API resources and regulate user and device access to specific endpoints, effectively reducing the attack surface and bolstering security.
4. API gateways
API gateways authenticate and authorise users using mechanisms like OAuth, JWT, and API keys, ensuring only authenticated users can access specific endpoints. They enforce role-based access control (RBAC) to check user permissions. To prevent abuse, they implement rate limiting and throttling, controlling request numbers and rates. API gateways route requests to backend services, balance loads across multiple instances, and enhance availability. They enforce security policies through IP whitelisting/blacklisting and TLS, protecting against attacks. Integration with WAF defends against web vulnerabilities. API gateways transform and validate data, sanitise inputs, and validate requests to prevent attacks. Logging and real-time monitoring aid in security analysis and threat detection. Caching responses reduces backend load and improves response times. Service discovery ensures traffic is routed to healthy instances. Lastly, API gateways handle token translation, ensuring proper credentials are used across services.
At A Glance
- Name: 4 network devices that secure API connections
- Type: Internet infrastructure institution
- Base: Global
- Profile focus: Institution
What It Does
- Public records support monitoring of its role, services, and key relationships.
Why It Matters
- Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
- Operational criticality: Medium
- Time horizon: Next quarter
What To Watch
- Monitoring focuses on verified service continuity, governance changes, and relationship signals.
Track verified source updates, role changes, and current public evidence.
Public-source signals support medium-impact monitoring for infrastructure visibility and dependency analysis.
Longer-term relevance depends on verified operating, policy, and relationship changes.
Member Briefing
Deeper Profile Context
Login is required to unlock the full profile briefing and source notes.
Only for Strategy Circle
Strategic Circle Access
Open to all readers. Unlock profile briefings after joining and logging in.
Join Strategic CircleOnly for Leadership Alliance
Leadership Alliance Access
For owners and management of IP-holding companies. Login required to unlock.
Join Leadership Alliance