Each trend page maps macro region signals into industry-level execution intelligence.

Market / Trends
Trends
Navigation is fixed as Trends -> Region -> Industry. Each region carries an intelligence summary page and each industry has a dedicated route for structured trend analysis.
Global plus five geographic routes aligned to the market taxonomy.
Cloud Service, Regional ISP, National Telecom, Datacenter, and Institutional.
Pages are designed for stable trend navigation rather than single-run article chronology.
Taxonomy
Trend Regions
Region
Global
Cross-region intelligence baseline and macro structural signals.
Region
North America
Execution speed, policy enforcement, and platform operating leverage.
Region
Europe and Middle East
Compliance-driven market adjustment and governance coupling pressure.
Region
Asia-Pacific
IPv4 scarcity economics, scaling demand, and operational modernization.
Region
Latin America and Caribbean
Connectivity expansion, regulatory transition, and asset-efficiency pressure.
Region
Africa
Governance normalization, infrastructure financing, and growth asymmetry.
Latest Coverage
Trends Headlines
Recogni launches new computing method for cutting costs
The system, called Pareto, improves the efficiency of the Al chip by simplifying its operation, thereby reducing power consumption.
What are the 4 basic types of firewall rules and why are they vital?
The role of firewall rules in network security are important, explaining how access control, network address translation, stateful packet inspection, and application-level gateways work together to protect networks from threats, manage traffic, and ensure compliance with security policies. Also read…
What is a host intrusion prevention system and how does it work?
HIPS is a critical security tool designed to protect individual computers by monitoring and analysing system behaviors to prevent unauthorised actions and potential threats. It complements traditional antivirus solutions by providing a proactive defense against evolving cyber threats, ensuring that …
Archive
Trends Article Archive
9,044 articles
Trends
Recogni launches new computing method for cutting costs
The system, called Pareto, improves the efficiency of the Al chip by simplifying its operation, thereby reducing power consumption.

Trends
What are the 4 basic types of firewall rules and why are they vital?
The role of firewall rules in network security are important, explaining how access control, network address translation, stateful packet inspection, and app…
Trends
What is a host intrusion prevention system and how does it work?
HIPS is a critical security tool designed to protect individual computers by monitoring and analysing system behaviors to prevent unauthorised actions and po…

Trends
GitHub CEO advocates for competition and open source in AI
OUR TAKEGitHub CEO Thomas Dohmke recently stresses the importance of maintaining competition within the AI industry to drive innovation and prevent monopolis…

Trends
Maxis and CMI join forces to supercharge 5G in Malaysia
Maxis and China Mobile International signed a MoU to enhance 5G deployment and develop innovative digital solutions.

Trends
Can Grammarly spot ChatGPT’s footprints?
Grammarly Authorship aims to help educators identify AI-generated text in student assignments by tracking real-time writing activities.

Trends
Nokia and TIM Brazil team up for 5G expansion
Nokia will supply TIM Brazil with advanced 5G equipment to enhance radio access network coverage in 15 states.

Trends
What are the differences between antivirus software and firewall protection?
Antivirus software and firewall protection are essential for safeguarding your computer and network from cyberthreats.
Trends
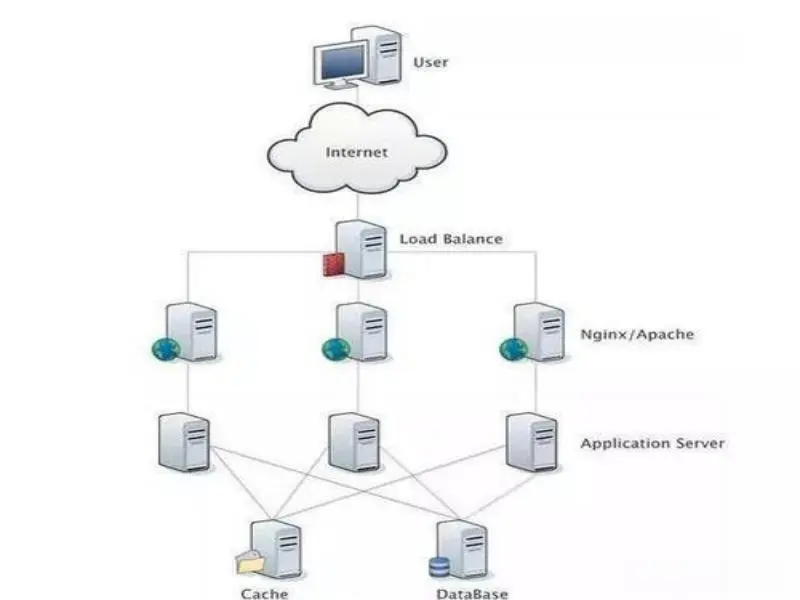
What is adaptive load balancing and why is it important?
Adaptive load balancing is crucial for organisations. Embracing it helps future-proof infrastructure against the digital world’s demands.

Trends
What is a f5 load balancer and why is it important?
Load balancing is crucial for network performance and scalability. The f5 load balancer is a key tool for many organisations’ IT strategies.
Trends
Sateliot expands 5G NB-IoT satellite constellation
Sateliot launches 4 LEO nanosatellites from Vandenberg AFB in California, advancing 5G NB-IoT NTN global connectivity mission.

Trends
6 types of network devices that use operating systems
The network devices are essential for communication and connectivity. They rely on operating systems to manage and control their functions.

Trends
Sateliot expands 5G NB-IoT satellite constellation again
Sateliot launched four more low-Earth orbit nanosatellites, thus enabling IoT capabilities on a global scale.

Trends
Singtel partners with Bridge Alliance to deliver GPU-as-a-Service
AIS, Maxis and Telkomsel will be the first telecommunications companies to offer this service in their markets.
Trends
Claude AI chatbot creator Anthropic sued for copyright infringement
A group of writers is suing AI startup Anthropic, by using pirated books to train its popular chatbot Claude.

Trends
Understanding enterprise architecture: Key features and benefits
In today’s rapidly evolving business landscape, organisations face the challenge of integrating complex technologies with dynamic business processes. Enter e…

Trends
Donald Trump shares fake AI-generated endorsement purportedly from Taylor Swift
OUR TAKEThe use of AI-generated images, such as those posted by Trump, can significantly influence voter perceptions and opinions. The proliferation of AI-ge…

Trends
ETF dealmaking continues as Bitwise acquires ETC Group
OUR TAKEBitwise Asset Management, a big player in the cryptocurrency exchange-traded fund (ETF) market, has announced it’s acquiring ETC Group, a London-base…

Trends
Host intrusion prevention: The key way to safeguard individual hosts
Host intrusion prevention is a cyber security strategy that identifies and blocks unauthorised actions on individual computers or servers. The rapid increase…
Trends
What are firewall rules? Essential directives for optimal network security
Firewall rules are essential for network security, determining how a firewall processes incoming and outgoing traffic. Firewall rules are applied sequentiall…
